The first step to securing your future
Protecting your people and premises is as important to us as it is to you. Whatever your security requirements, we’re with you every step of the way.

Visitor management

Thought leadership

Access control

Visitor management

Press release
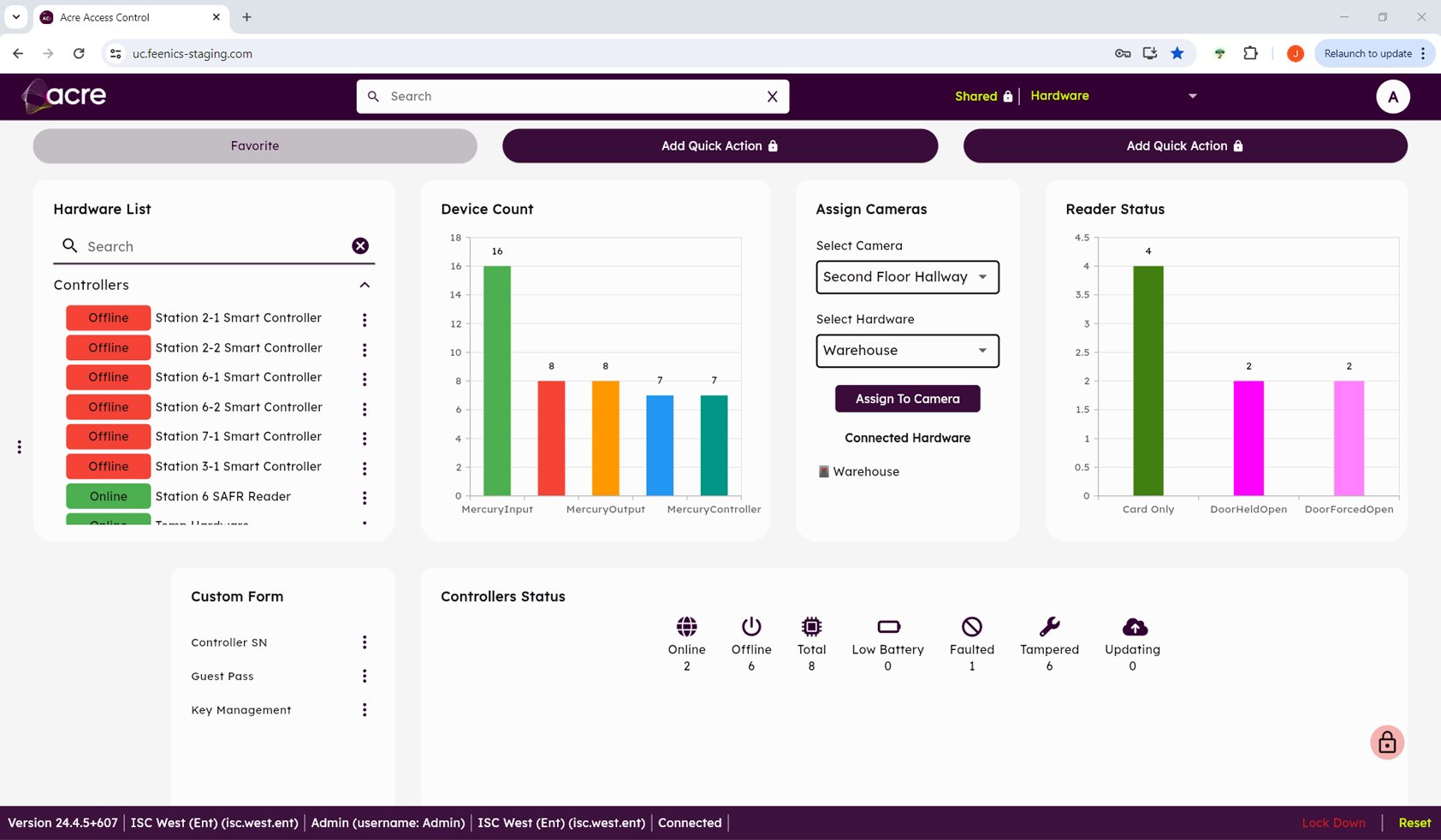
Access control

Intruder alarms

Visitor management

Thought leadership

